SlowMist: Руководство по устранению неполадок и усилению безопасности учетной записи X
Original author: Yao
Background Overview
Recently, there have been many cases where the X accounts of Web3 project owners/celebrities have been stolen and used to send phishing tweets. Hackers are good at using various means to steal user accounts. The more common routines are as follows:
-
Induce users to click on fake Calendly/Kakao meeting reservation links to steal user account authorization or control user devices;
-
Private messages trick users into downloading programs with Trojans (fake games, conference programs, etc.). In addition to stealing private keys/mnemonics, Trojans may also steal the permissions of account X.
-
Use SIM Swap attack to steal the permissions of X account that relies on the mobile phone number.
The SlowMist security team assisted in solving many similar incidents. For example, on July 20, the account X of the TinTinLand project was stolen, and the attacker pinned a tweet containing a phishing link. With the assistance of the SlowMist security team, TinTinLand promptly solved the account theft problem and conducted authorization review and security reinforcement for the X account.

Considering the frequent occurrence of victims, many users do not know how to enhance the security of X account. In this article, the SlowMist Security Team will explain how to perform authorization check and security settings for X account. The following are the specific steps.
Authorization Troubleshooting
Let’s take the web version as an example. After opening the x.com page, click “More” in the sidebar and find the “Settings and privacy” option, which is mainly used to set the security and privacy of the account.


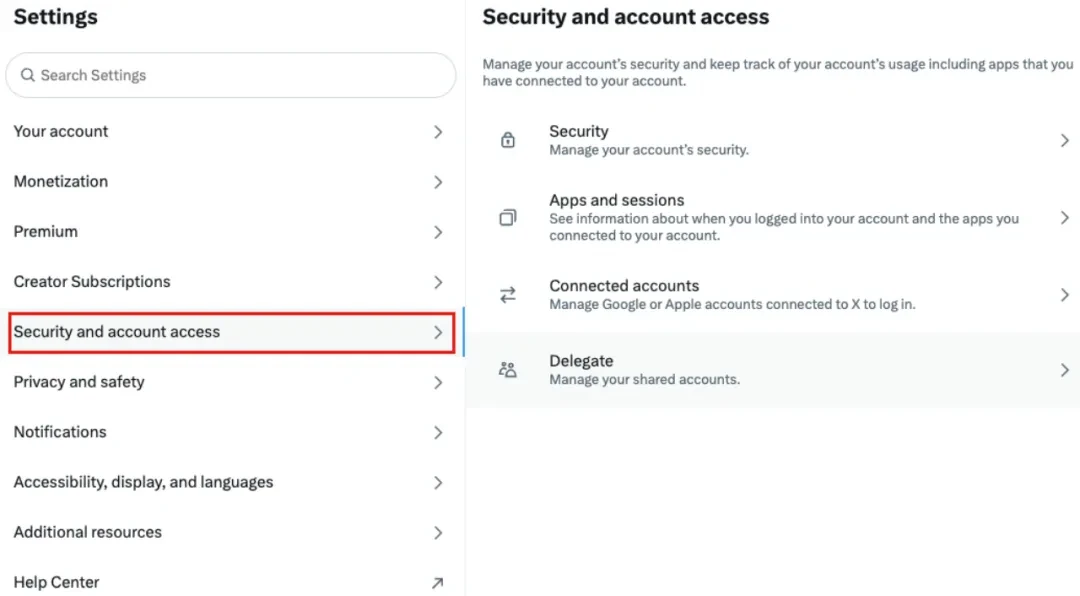
After entering the Settings column, select Security and account access to set up account security and authorized access.
View authorized приложения
Many phishing methods take advantage of users mistakenly clicking on an authorized application link, which results in the authorization of the tweeting permission of account X, which is then used to send phishing messages.
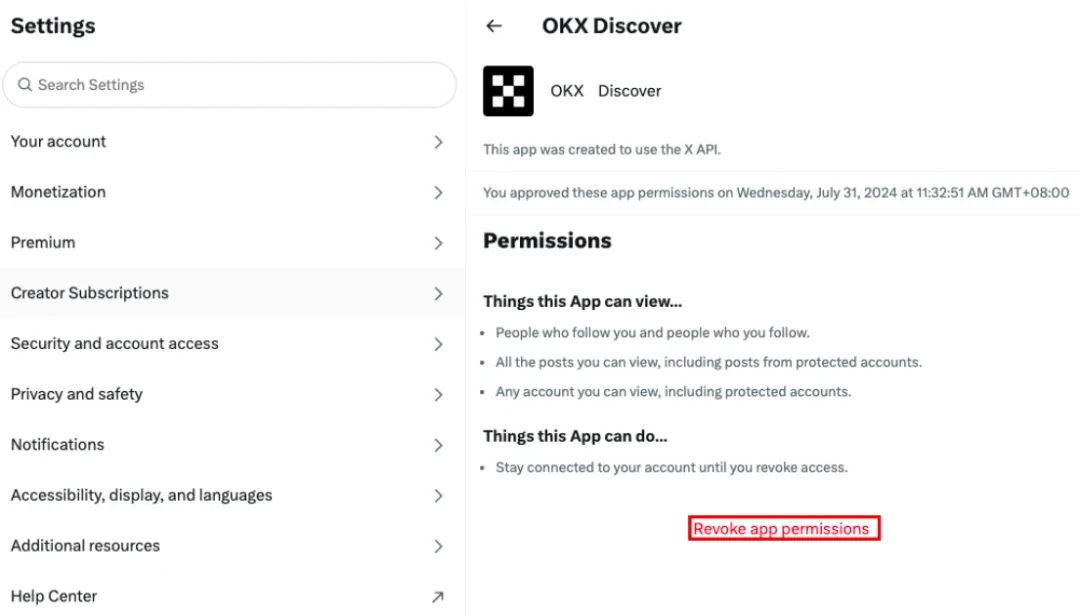
Troubleshooting method: Select the Apps and sessions column to check which applications the account has been authorized to. As shown in the following figure, the demo account has been authorized to these three applications.

After selecting a specific application, you can see the corresponding permissions. Users can remove permissions through Revoke app permissions.
View the entrustment status
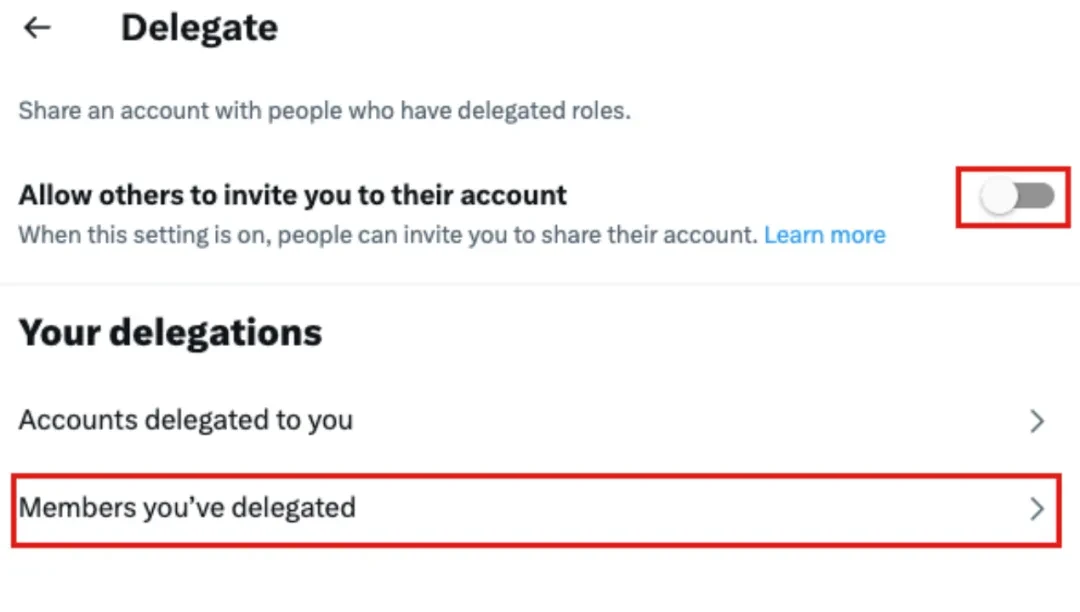
Troubleshooting method: Settings → Security and account access → Delegate

If you find that the current account has enabled invitation management, you need to go to Members youve delegated to check which accounts the current account has been shared with. If sharing is no longer needed, you should cancel the delegation as soon as possible.
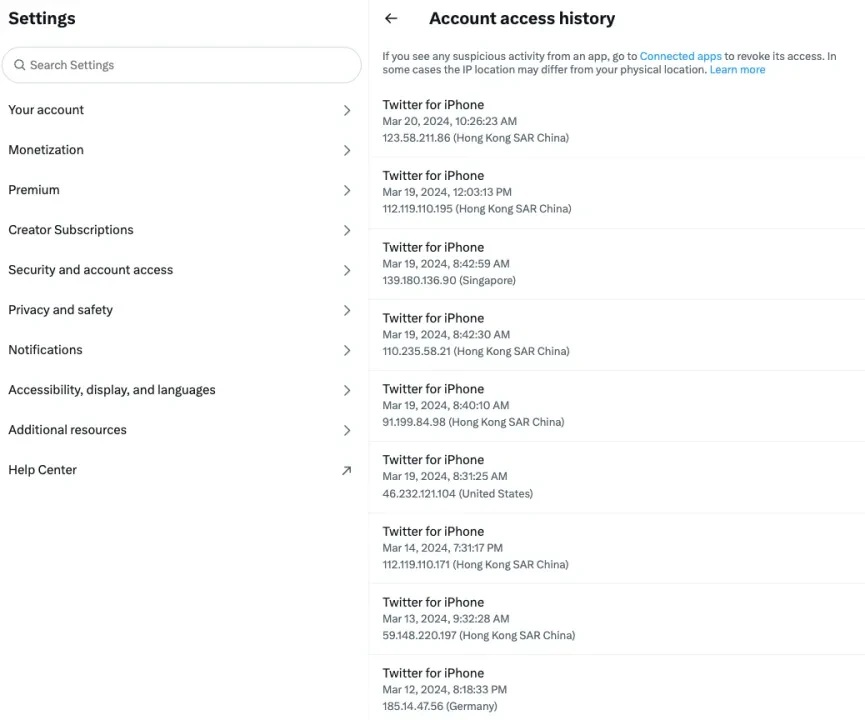
View abnormal login logs
If the user suspects that the account has been maliciously logged in, the user can check the login log to view the device, date and location of the abnormal login.
Troubleshooting method: Settings → Security and account access → Apps and sessions → Account access history
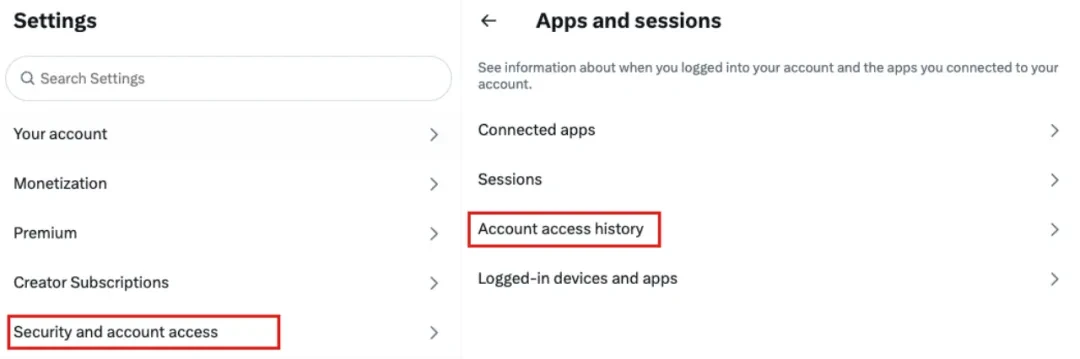
As shown in the figure below, enter Account access history to view the model of the login device, login date, IP and region. If abnormal login information is found, it means that the account may have been stolen.
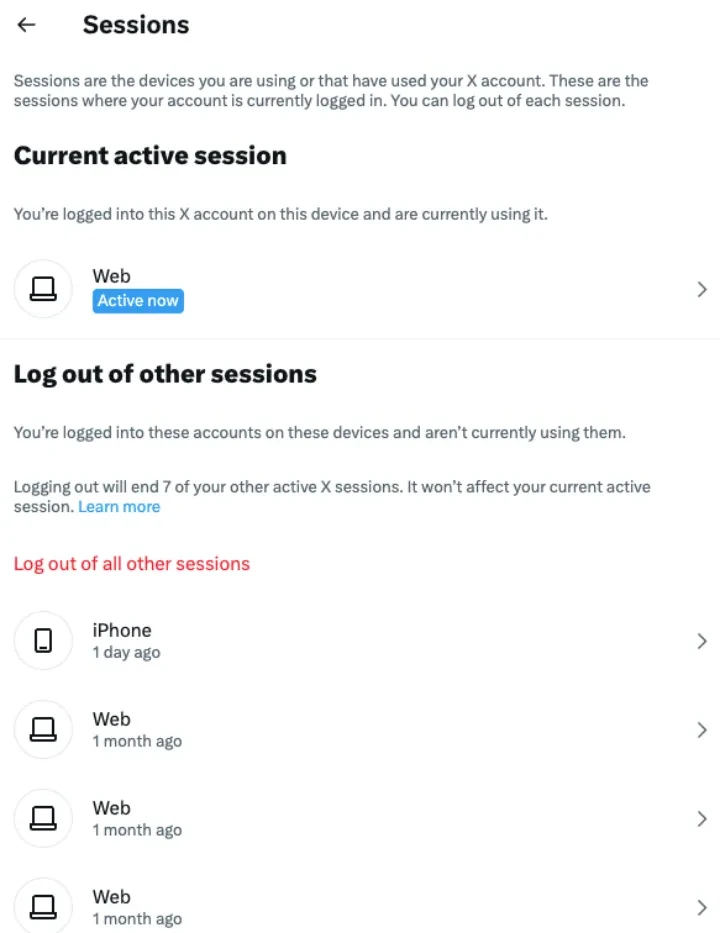
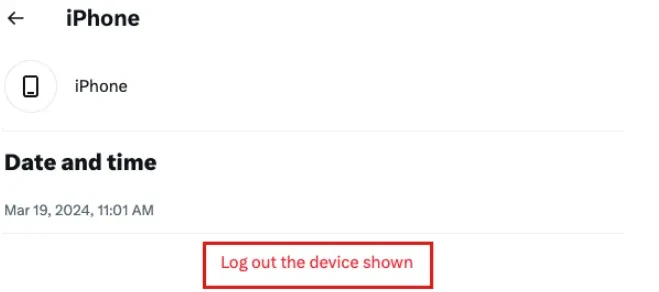
View Login Devices
If a malicious login occurs after the X account is stolen, the user can check the login devices of the current account and then kick the malicious login device offline.
Troubleshooting method: Select Log out the device shown to log out of the account from a device.
Security Settings
2FA Authentication
Users can enable 2FA verification to provide double verification insurance for their accounts, thus avoiding the risk of their accounts being directly taken over after password leaks.
Configuration method: Settings → Security and account access → Security → Two-factor authentication
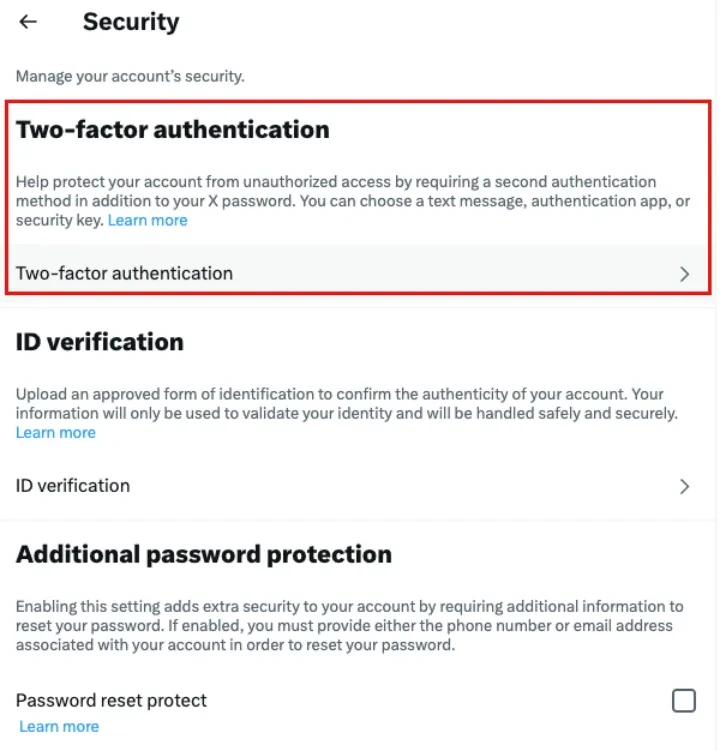
You can set up the following 2FA to enhance the security of your account, such as SMS verification code, authenticator and security key.

Additional password protection
In addition to setting account passwords and 2FA, users can also enable additional password protection to further enhance the security of their X accounts.
Configuration method: Settings → Security and account access → Security → Additional password protection

Подведем итог
Regularly checking authorized applications and login activities is the key to ensuring account security. The SlowMist security team recommends that users regularly perform authorization checks on X accounts according to the troubleshooting steps to enhance account security and reduce the risk of being hacked. If you find that your account has been hacked, please take immediate measures to change the account password, conduct authorization checks, revoke suspicious authorizations, and set up security enhancements for the account.
This article is sourced from the internet: SlowMist: X Account Security Troubleshooting and Reinforcement Guide
Related: Boshi HashKey Bitcoin and Ethereum ETFs both top the Asian market
Hong Kong, July 5, 2024 – Yesterday, Boshi HashKey Virtual Asset ETF achieved a historic breakthrough, with total assets under management exceeding US$110 million for the first time. Among them, Boshi HashKey Ethereum ETF (HK.3009) has a clear advantage, with holdings remaining stable at more than 6,000 Ethereum since May 7, continuing to lead the market. Following closely, Boshi HashKey Bitcoin ETF (HK.3008) also surpassed yesterday, with the scale of management exceeding US$90 million, jointly pushing the total scale of Boshi HashKey Virtual Asset ETF to a record high, currently ranking first in Asia. Since 2015, the founding team of HashKey has been deeply involved in the construction of the global blockchain and crypto ecosystem. As one of the few forward-looking institutional investors in the world, HashKey not only funded…







