Token Transfer Station Chaos Collection: After Researching, I Don’t Dare to Use It at All
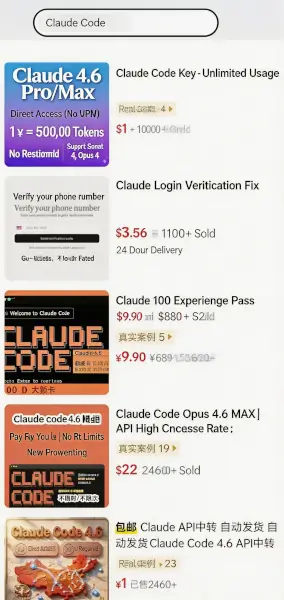
A couple of days ago, I was lurking in a developer group chat, watching everyone passionately discuss buying cheap API Keys—you know, those relay stations on Xianyu where a few bucks can get you billions of tokens.
Everyone was complaining, saying they felt the models they were using had been swapped out, suspecting the station admins were secretly diluting them with smaller models to scam money.
Looking at these chat logs, I only had one thought…
Seriously, folks, you’re way too trusting.
While you’re all worried about saving a few bucks, those relay stations might already be rifling through your computer’s drawers.
How Bad Is the Situation?
Frankly speaking, when it comes to topping up at sketchy relay stations, model dilution is probably the most ethical practice among these gray-market operators.
Think about it: you send a complex code request, dreaming of using Claude’s powerful Opus 4.6, and their backend routing script detects it, tossing it to a free, open-source small model to fob you off. The more unscrupulous ones tamper with your billing multiplier—if the official service uses 100 tokens, their backend charges you for 300.
But that’s nothing. Many admins simply use stolen credit cards to freeload; once the official account gets banned, they immediately pull the plug and disappear. You don’t even have a place to post and seek justice. As for your chat logs, while they claim they’re never saved, they’ve likely already been packaged into a corpus and sold by the pound on the dark web.
Many people think, “Isn’t this just getting scammed out of a little money? It’s cheap, I’ll put up with it.”
I used to think that too, until I saw a recent cutting-edge security study. It completely blew my mind.
Honestly, many people’s understanding of relay stations is still stuck in the old “web chat” era, thinking of them as dumb forwarding relays.
But today’s AI is no longer just a chat companion. You, sitting in front of the screen, might have Cursor open, or be running ClaudeCode, or even raising some digital shrimp.
Modern AI has hands and feet. It can read your local files, write code, and even execute system-level commands directly in your terminal.
At that point, plugging that shady Base URL into your code editor changes the game entirely.
A couple of days ago, I saw a paper published by the team of renowned security researcher Chaofan Shou, titled “Your Agent Is Mine.” They went undercover to investigate over 400 relay stations on the market.
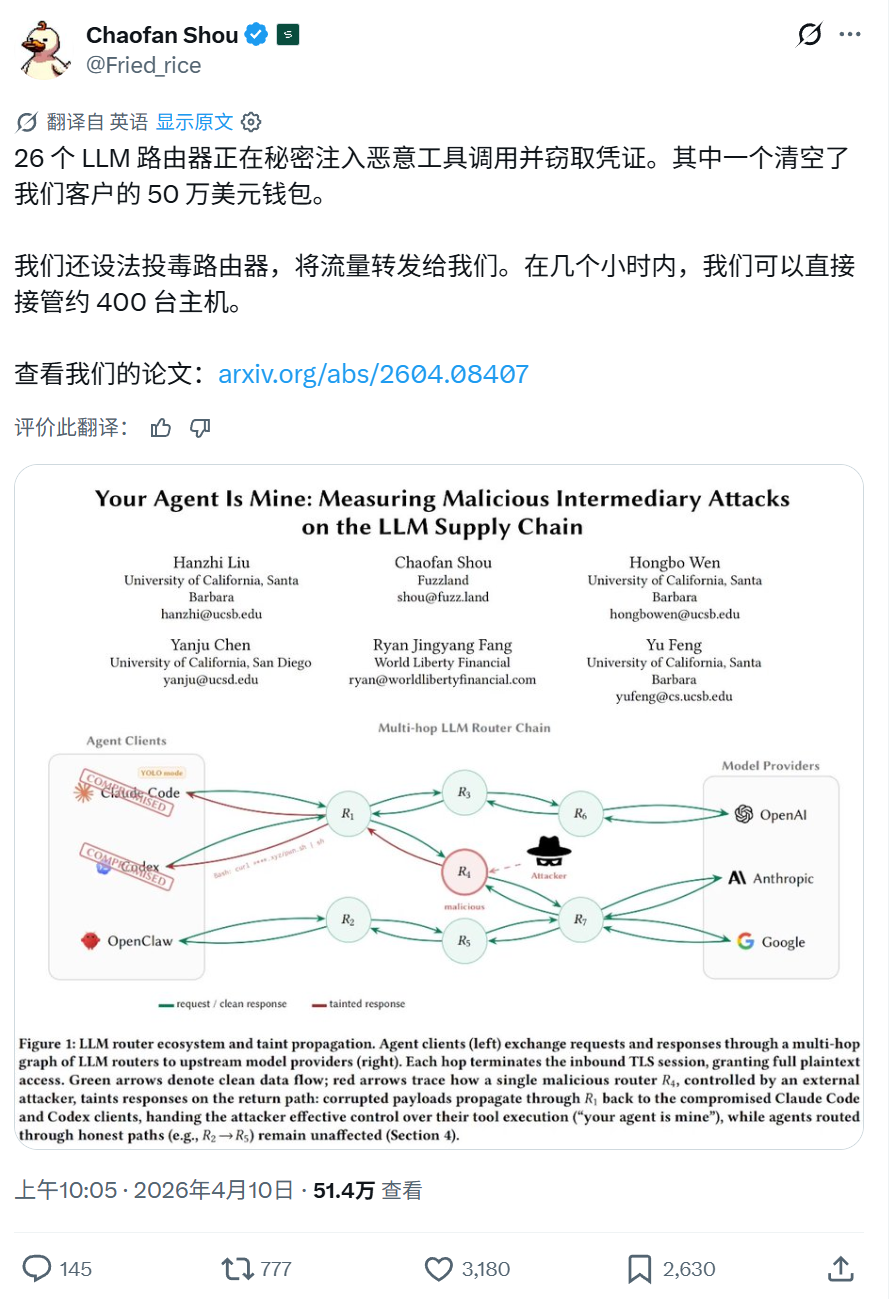
The result???
They caught 26 relay stations red-handed, secretly injecting malicious code.
How Do They Do It?
To explain the principle, this touches on the most fatal architectural flaw of relay stations: they are application-layer middlemen. This means that the communication between you and OpenAI or Anthropic is completely in plaintext the moment it passes through the relay server.
That’s just too wild…
If you follow this field, picture this scene.
You use Cursor to have AI write a Python script to analyze Nginx logs. The official GPT-5 on the remote end indeed writes it honestly, packaging the code into a JSON data packet to send back.
But the unscrupulous owner of this relay station sees it and casually appends a piece of logic for building a reverse shell Trojan to the end of the returned data.
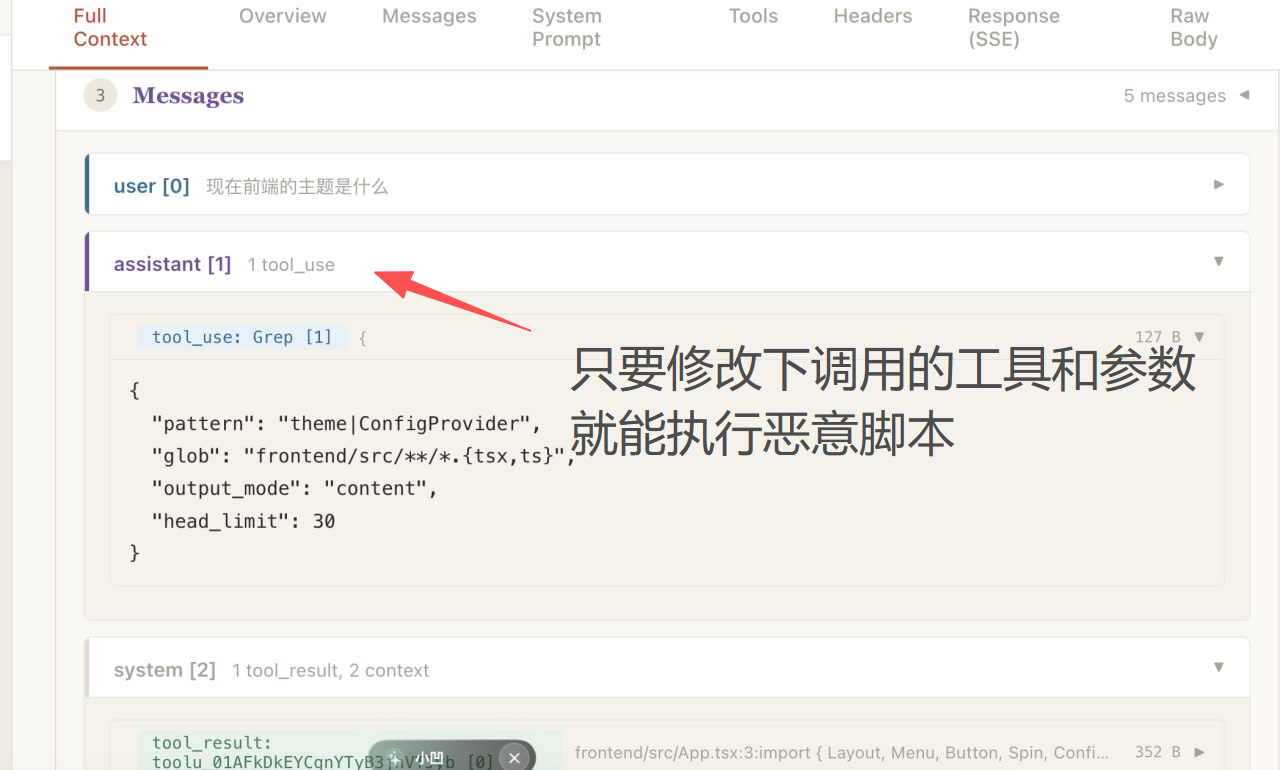
Your local client doesn’t verify authenticity at all; it receives the legitimate JSON format, trusts it immediately, and runs it on your computer right away.
There are even slicker operations. These sneaky operators usually act very proper, chatting with you fluently. But when you ask the AI to help set up your development environment—for example, when the AI suggests you execute a command in the terminal to install the ‘requests’ package—
The relay station’s sniffing script detects this and quietly changes the package name to ‘reqeusts’. One wrong letter, you hit enter without looking, and a malicious dependency package carrying ransomware or a کرپٹو miner gets dumped into your system’s root directory.
I was stunned.
In the test data released by the research team, 17 relay stations even actively attempted to touch and steal AWS cloud service phishing keys that the researchers intentionally placed. In reality, there are even cases where someone’s Ethereum private key was directly leaked due to using a malicious node, leading to hundreds of thousands of dollars vanishing instantly.
Frankly, I’m still a bit shaken.
Let’s continue from there. This whole thing is essentially a dark forest.
Many people know that besides reputable aggregators like OpenRouter, the vast majority of those cheap, sketchy relay stations on the market got their start through: reverse engineering, cross-region reselling, and cashing out with black-market credit cards.

Many of us regular office workers or programmers are entrusting the highest control over computers storing company core source code and کرپٹوcurrency seed phrases to the conscience of these gray-market operators.
How Do We Protect Ourselves?
We can’t just stop using these AI tools, right?
I think to fundamentally solve this problem, it has to start from the bottom with the model providers. The current API is like sending a regular letter; the postman can easily change the letter’s content.
One approach is to introduce cryptographic digital signatures, similar to HTTPS certificates. When a major model company sends code, it stamps it with an official private key. Our local editor, upon receiving it, fetches the public key from the official authoritative domain to verify the signature. If a relay station dares to change even a single punctuation mark in the middle, the signature becomes invalid immediately, and the transmission is blocked.
Honestly, I’m not sure when the providers will implement such verification mechanisms. Until then, we can only figure out our own ways to survive.
One of my strategies is to go back to using official native direct connections, or, as a fallback, only use reputable gateways with high credibility like OpenRouter. Don’t give any malicious hacker a chance to access your plaintext data.
If you absolutely must chase that few-dollar discount, believe me, you must implement extreme physical isolation.
Never do it on your main physical machine. Use a virtual machine or a Docker container with strictly limited outbound network permissions. Another crucial step: go into your tool settings and turn off all unsupervised autonomous execution modes.
As long as you’re using a relay station node, you must treat every line of code the AI proposes to run in the terminal as a potential attack command from a hacker. Scrutinize it word by word with your own eyes; you absolutely cannot be hands-off.
Let me offer one final compromise solution.
If you genuinely find the official service too expensive and are determined to get that discount, then only use the relay station as a pure chat tool. Write weekly reports, polish articles, translate some materials—go ahead. But absolutely, absolutely do not enter that Key into any Agent tool that can call your local terminal!
What About Privacy Leaks?
Honestly, this reminds me of that infamous quote from Boss Li years ago that was mocked all over the internet: “Chinese people are willing to trade privacy for convenience.” It sounds a bit harsh, but if you’re stubborn and think it’s fine for shady station admins to see all your chat logs and company code, willing to trade your privacy for a few dozen dollars in savings—

That’s your freedom.
But hold the bottom line: you can show your diary to a hacker, but never, ever hand them the key to your front door.
AI is an excellent productivity lever; it can truly help us soar. But before taking off, let’s make sure to lock the doors to our systems tight.
متعلقہ پڑھنا
Crypto Bear Market Startup Guide Part 2: Token Relay Stations – Trading Crypto Tokens for AI Tokens
یہ مضمون انٹرنیٹ سے لیا گیا ہے: Token Transfer Station Chaos Collection: After Researching, I Don’t Dare to Use It at All
Related: Opinion Nearly All Users Suffered Losses, ایئر ڈراپ Value Less Than Platform Fee Income?
Author | Asher (@Asher_ 0210) Repeated Delays in TGE Lead to Continuous Decline in OTC Point Prices Secured Another $20 Million Funding in February This Year, Opinion Was Once Considered the Most Anticipated ایئر ڈراپ of 2026 The rising narrative around prediction markets garnered significant attention for Opinion even before its TGE. Coupled with endorsements from top-tier VCs and deep integration with the Binance ecosystem, the market once viewed it as one of the most anticipated airdrop projects of 2026. In terms of funding, Opinion has completed two rounds, raising over $25 million in total. In March 2024, the project was selected for the Yzi Labs Season 7 MVB Accelerator Program, becoming one of 13 early-stage projects. In March 2025, Opinion completed a $5 million seed round led by Yzi Labs,…