From the Kelp DAO Incident to Verifiable UI: Why a “Verifiable Interface” Could Be the New Decentralized Security Baseline?
On April 18, an attacker exploited Kelp DAO’s LayerZero routing configuration, which used a 1-of-1 DVN without optional verifiers, to forge cross-chain messages. This caused the contract to incorrectly release 116,500 rsETH. Depending on different loss-sharing scenarios, the potential bad debt range for Aave is estimated between $123.7 million and $230.1 million.
Objectively speaking, this is not only the largest DeFi security incident since 2026, but more importantly, it has shattered an architectural assumption that the entire industry had previously tacitly accepted: In pursuit of efficiency, liquidity, and yield, an increasing amount of security has been quietly bet on a small number of implicitly trusted intermediary layers.
1. The Kelp DAO Incident: The Breakdown of Decentralized Mechanisms
If we only interpret the Kelp DAO incident as just another common on-chain security mishap, it’s easy to underestimate its significance as a warning about the structural risks within the entire DeFi ecosystem.
As a Liquid Restaking protocol within the Ethereum ecosystem, Kelp DAO theoretically allows users to deposit ETH and receive rsETH as a receipt. This receipt can not only circulate on the mainnet but is also wrapped via LayerZero’s OFT standard and deployed across over 20 chains, including Base, Arbitrum, Linea, Blast, Mantle, and Scroll.
इस का मतलब है कि the cross-chain contract on the Ethereum mainnet holds all the ETH reserves, while the rsETH on other chains are essentially just “withdrawal slips” for the mainnet reserves. This implies the system’s fundamental premise is the anchoring relationship that “the amount locked on the mainnet must always be greater than or equal to the amount minted on L2 chains” cannot be broken.
What the attacker breached was precisely this seemingly simple yet extremely critical underlying constraint. He directly forged a “legitimate” LayerZero cross-chain message, tricking the mainnet bridge contract into believing it was a compliant redemption instruction from another chain, thereby releasing 116,500 rsETH.
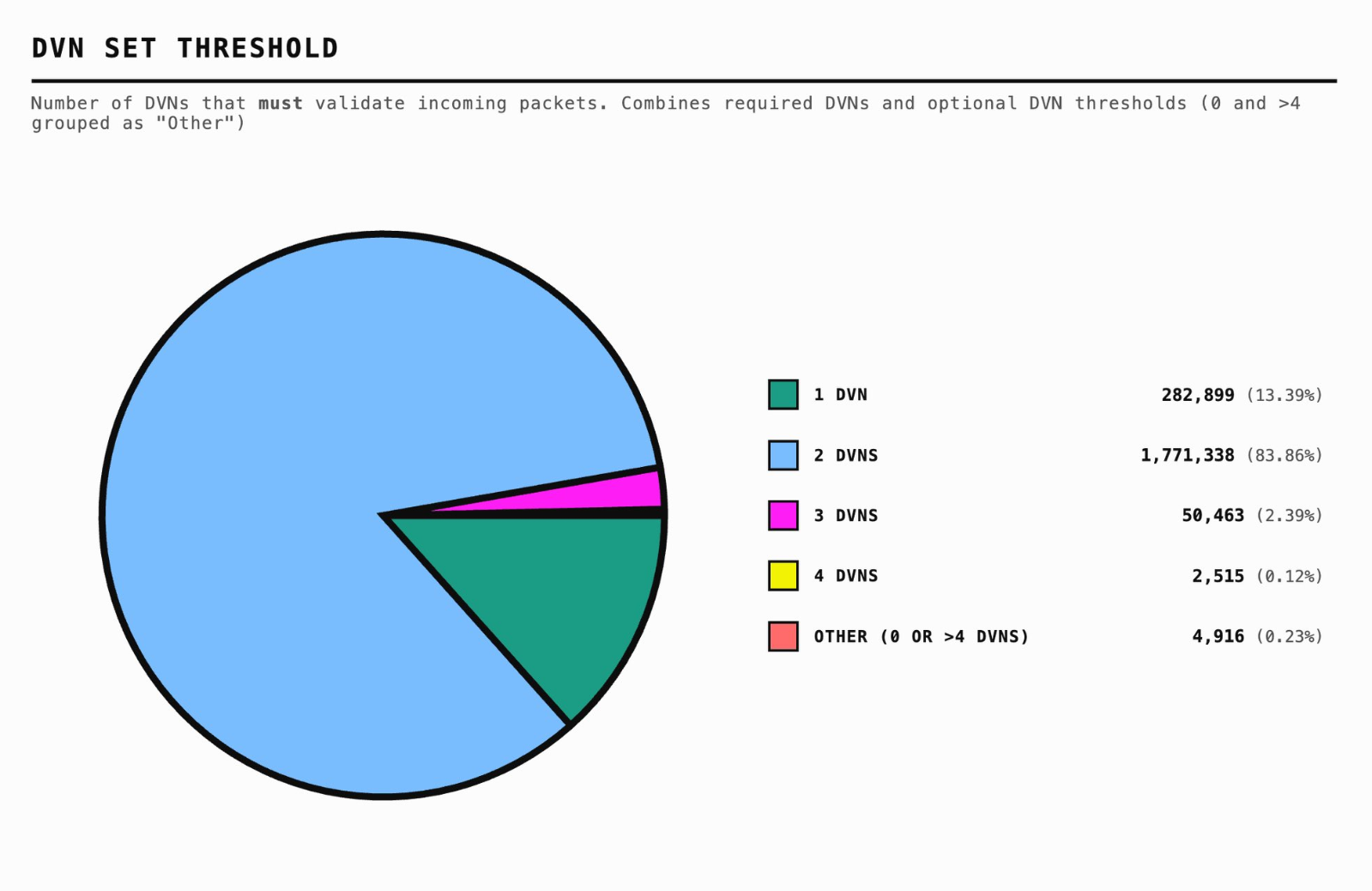
The crux of the issue lies within LayerZero’s verification configuration. Kelp DAO adopted a 1/1 DVN (Decentralized Verifier Network) configuration, meaning a signature from a single verification node was sufficient to release a cross-chain message! LayerZero officially recommends a 2/2 or multi-verifier redundancy. The risk of this 1/1 configuration was publicly highlighted by security researchers as early as January 2025, yet it remained unaddressed for 15 months!
This is why this incident cannot be easily categorized as “a bridge getting hacked” or “a protocol’s risk control being insufficient.” What it reveals are two layers of overlapping single points of failure:
- Layer 1: Verification Single Point of Failure. DVN is theoretically designed as a composable X-of-Y-of-N security model, supporting multiple independent verifications for different security needs. However, in Kelp DAO, the legitimacy of an entire message was compressed into a single assumption: “one verification node will not fail.”
- Layer 2: Reserve Single Point of Failure. Once this mainnet reserve pool is compromised, rsETH on other chains instantly cease to be cross-chain assets, exposing their true nature as IOUs anchored solely to a single mainnet point.
When the verification single point of failure and the reserve single point of failure combine, the risk no longer remains within a single protocol but spills outward along the composability rails of DeFi.
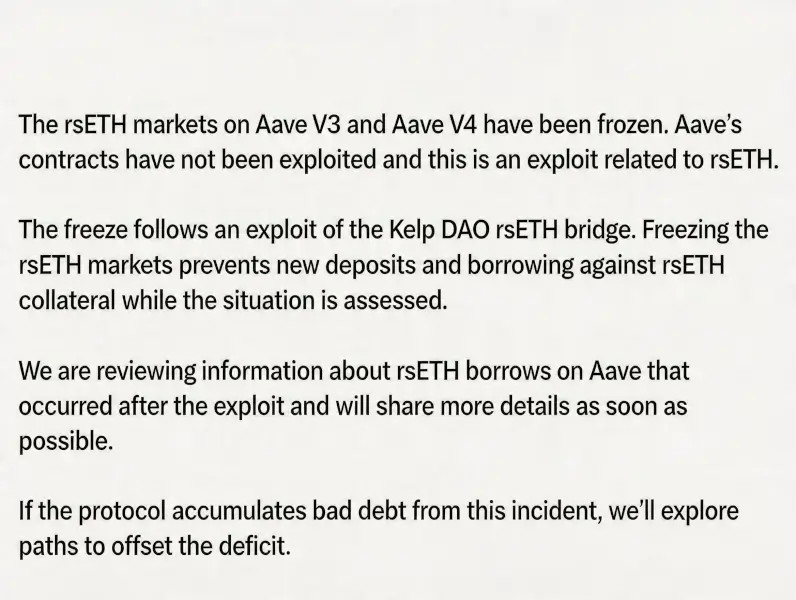
This is why Aave urgently froze the rsETH/wrsETH markets on multiple chains after the incident, adjusted the WETH interest rate model, and subsequently froze several WETH markets to prevent pressure from spreading to more assets. Although Aave itself was not hacked, the distorted collateral, blocked liquidations, and borrowers’ health factors being on the edge ultimately exposed the protocol to substantial bad debt risk.
Zooming out, we find that this logic of “outsourcing security to a single point” exists not only in bridges and verifiers but also lurks in a place users encounter daily, yet is rarely discussed openly: the interface.
2. From “Asset Self-Custody” to “Verifiable Interaction”: The Most Overlooked Single Point of Trust
The Web3 community has a long-standing adage: Don’t trust, Verify.
Ethereum’s official explanation for running a node is quite straightforward: Running your own node means you don’t have to trust the results others tell you, because you can verify the data yourself, instead of outsourcing your judgment of the network’s truth to centralized data providers.
This principle holds equally true for wallet and DeFi interactions.
Non-custodial wallets like imटोकन are essentially tools for users to access their accounts – a window to “see assets, send transactions, and log into applications.” The wallet itself does not custody your funds, nor does the platform hold your private keys. Over the past few years, the industry has gradually come to accept the importance of “asset self-custody.” More and more people understand that true decentralization isn’t just about putting coins on the chain; it’s about returning control of assets to the users themselves.
However, the problem lies in the fact that while we increasingly emphasize “self-custody” at the asset level, we still largely default to a more subtle form of outsourcing at the interaction level. We delegate the understanding of transaction meaning, the judgment of call results, and the trust in the interface’s authenticity to the frontend layer presented to us.
This is precisely the most easily overlooked risk in DeFi today: Is the transaction a user signs truly the one they think they are signing?
In everyday on-chain interactions, users almost never interact directly with the chain itself but with layer upon layer of packaged interfaces. Examples include a DApp’s web frontend, wallet pop-ups, and path descriptions from aggregators. In the future, this will also include Agent-generated calls and result confirmations. These interfaces tell you: “You are depositing 100 ETH into this strategy,” “You will receive this APY,” “You are only performing a routine approval.”
But what is the actual calldata that gets signed, broadcast, and executed on-chain? Is the frontend description strictly consistent with the underlying execution? The vast majority of users lack the ability to independently verify this.
This is why historically recurring issues like frontend hijacking, address replacement, and malicious authorization disguises – while appearing as different types of security incidents – all point to the same underlying problem: the user did not sign the transaction they thought they were signing.
From this perspective, the Kelp DAO incident exposes not just the single-point verification problem in the bridging path. It also serves as a timely reminder to the entire industry about another long-underestimated fact: in many on-chain interactions, the interface itself is a default trusted but rarely verified single point of failure. The moment you click “Confirm,” you are betting the correctness of that call on the premise that “the interface is not lying.”
This leads us to the concept of “Verifiable UI.”
The so-called “Verifiable UI” is exactly what it sounds like. Its core is not about making the frontend prettier or the signature pop-up more user-friendly, but rather about establishing a verifiable connection between what the interface displays and the actual call being executed on-chain – a connection that can be checked by the user, verified by the wallet, and audited retrospectively.
In other words, it aims to solve not “whether information is displayed,” but “whether the displayed information truly corresponds to what is about to happen on-chain.” This means:
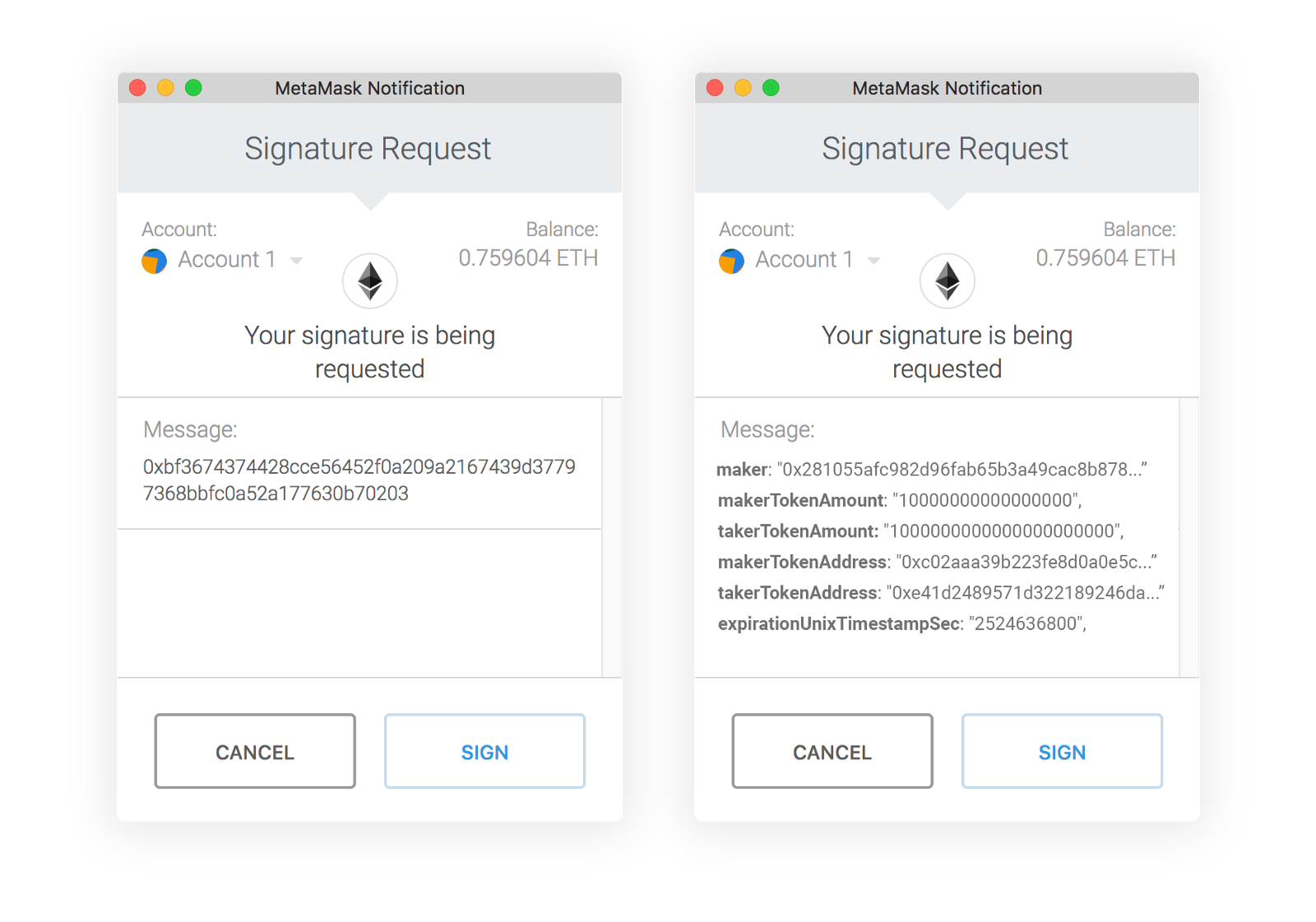
- Before signing, the wallet should not just show the user a hexadecimal string or merely relay a description text unilaterally generated by the frontend. Instead, it should decode the calldata into a human-readable, semantically clear operational intent.
- Every step described by the interface should be mappable to verifiable evidence on-chain, rather than remaining within a logic of interpretation that only holds true if “the user believes it.”
- Only then can the cognitive gap between “what you think you are doing” and “what is actually happening on-chain” be bridged.
Once this is established, the interface is no longer a pane of glass that users can only passively trust but never independently verify. It becomes more like an execution manual that users can personally confirm and trace back to later.
Looking at DeFi today, interface verifiability remains a severely underestimated topic. However, extending the timeline slightly, it will quickly evolve from a “worthwhile security optimization to discuss” into a “core capability that can no longer be delayed.” This is because the path of Ethereum interaction is undergoing a quiet yet profoundly significant migration.
3. Why Verifiable UI is Becoming the New Security Frontier
If the Kelp DAO incident exposed the long-standing single-point trust issues within the older generation of DeFi architecture, “Verifiable UI” corresponds to a new phase that has already begun to arrive.
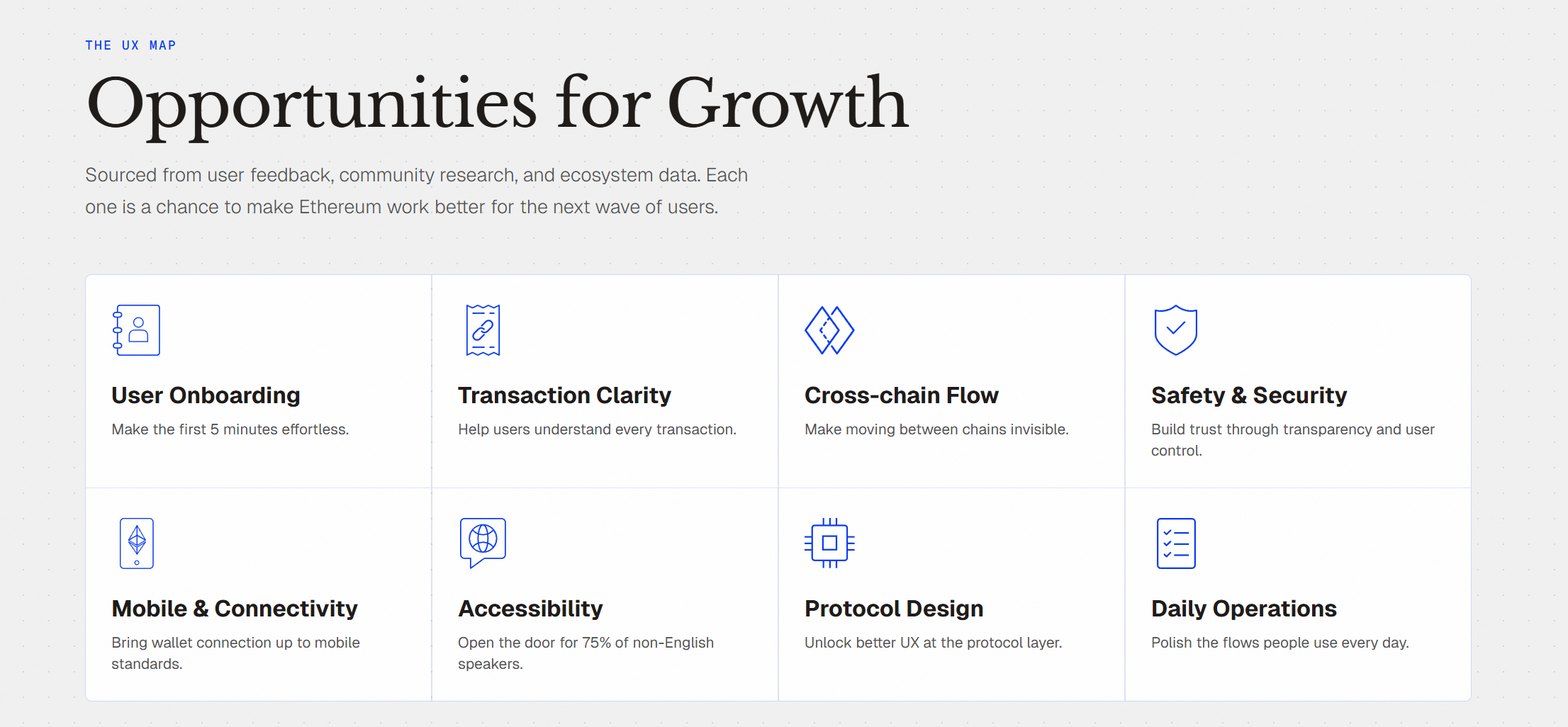
The ETHUX map of Ethereum UX clearly outlines the core pain points of today’s on-chain interactions. Transaction Clarity, Cross-chain Flow, and Safety & Security have always been the most critical pain points. Issues like blind signing, signing fatigue, bridging pain, and asset fragmentation are familiar to almost every veteran user.
This indicates not that “user education is insufficient,” but a more fundamental truth: in the on-chain world, UX and security have never been separate things.
In other words, often, not understanding is itself the biggest security risk.
As the interaction paradigm shifts from “users clicking step-by-step within a DApp frontend” to “users expressing intent, and the system automatically executing it,” this problem will only be amplified, not diminished.
After all, in the traditional DApp frontend era, users could at least see buttons, pages, and approval pop-ups. Even if their understanding was incomplete, they could vaguely perceive “I am performing several steps,” “This is an approval or a transfer,” “I am bridging or depositing.”
But once we enter the Agent era, this visible sense of process will be greatly compressed. Users will no longer click through Router, Bridge, Vault, and Lending बाज़ार interfaces to confirm each step. Instead, they are more likely to tell an AI wallet: “Switch my ETH to a safer yield strategy,” “Bridge to Base with max slippage control,” “Only allow this Agent to spend 100 USDT within 24 hours,” and then wait for a “Completed” result.
This certainly implies a massive efficiency gain. But it also means that the intermediary paths, parameters, approvals, and execution sequences are increasingly folded out of the user’s sight. It is against this backdrop that imटोकन proposed two parallel directions: one is to continue exploring intent-based interaction paths, where users only express “what they want” and the system handles the pathfinding and execution; the other is to advance “Unified & Verifiable UI,” elevating the fact that “the interface itself can become an attack surface” into a long-term product-level proposition.
This highlights the most critical change in the role of next-generation wallets.
In the past, wallets functioned more like signing tools, responsible for sending the user’s confirmation action to the chain. As Agents gradually integrate into the interaction flow, the wallet can no longer just be a channel. It must become the final checkpoint for certainty before execution. The AI can handle understanding requirements, generating solutions, and planning paths. But the wallet must be responsible for translating these probabilistic generative results into deterministic execution content that users can verify, systems can validate, and rules can constrain.
In this sense, “Verifiable UI” corresponds not to a more advanced interface design concept, but to a new model of interaction security. It could even be said that it is an almost essential foundational piece that self-custody wallets must put in place as they enter the next phase.
The industry has long emphasized “Not your keys, not your coins.” But in the era where intent-driven and Agent-executed interactions are becoming mainstream, we must add another line: Your interface should also be an interface you can verify.
अंतिम विचार
Following the Kelp DAO incident, the industry quickly saw a flurry of discussions regarding DVN configurations, LRT risk controls, bridging paths, and single-point risk audits.
These discussions all have their value.
However, if an incident costing hundreds of millions of dollars ultimately concludes with “who configured the multi-sig with fewer signers this time,” then it has not been truly understood. To put it bluntly, the efficiency, liquidity, and yield of many on-chain products today are still built upon single-point assumptions that users cannot see or verify.
This is why decentralization has never been the antithesis of efficiency; it is the baseline for security.
The era of building security on single-point assumptions truly needs to end.
यह लेख इंटरनेट से लिया गया है: From the Kelp DAO Incident to Verifiable UI: Why a “Verifiable Interface” Could Be the New Decentralized Security Baseline?
Introduction Pump.fun launched in early 2024 as a permissionless Meme Launchpad on Solana, allowing anyone to create and trade tokens within seconds via a Bonding Curve mechanism. Starting as a niche experiment, it quickly became one of the highest-revenue applications on any public blockchain. From 2024 to 2025, Pump.fun’s daily protocol revenue consistently matched or even surpassed that of Hyperliquid, a fact made more notable by the inherently cyclical nature of the Meme market it operates in. Its native token, $PUMP, was issued at $0.004 through a $600 million ICO, with an FDV of $4 billion. Over the past few months, revenue has hit record highs and the token’s value has doubled, yet the current price of $PUMP is around $0.0019, down approximately 80% from its all-time high of $0.086…